Blog
3 things you can do to make sure your data security doesn’t take a summer vacation
Summer mode, the time of year when “summer hours” and summer vacations are happening, is upon us. It’s easy to think more about how you’re going to get out and […]
If you haven’t done your spring cleaning yet, Science says it will make you happier after it’s done
No pressure, but seriously, we’re approaching June, and it’s almost embarrassing that we’re talking about Spring cleaning. But we also know that the weather has been terrible in the upper […]
What is happening inside U.S. Recycling bins?
We promised to keep you updated on what’s happening in recycling bins around the U.S., and there are some changes that are turning heads. As the New York Times reported […]
Plastic is plastic, right?
If it’s plastic, you can recycle it, right? Not exactly. In fact, there are certain types of plastic that have never been recyclable. Do you know what your city will […]
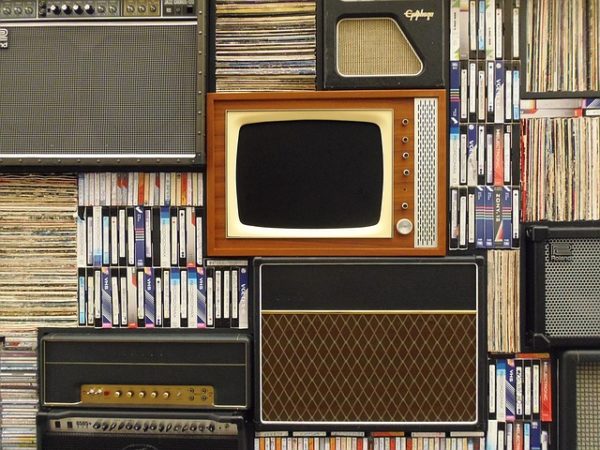
I have old VHS and Betamax tapes taking up space in my house. What should I do with them?
Are VHS or Betamax tapes taking up valuable storage space in your home? Do you want to clear them out but have no idea what you should do with them? […]
Sustainability for the school season
Post-Labor Day in Minnesota means one thing – it’s back-to-school season! We believe September’s return to school is another excellent opportunity to practice sustainability during the year. To get you […]
Debunking 3 sustainability misconceptions
Our partnership with our parent company, Rohn Industries, means that we are serious when we talk about making the earth a better place. Making an effort to live more sustainably […]
How to keep your company data secure when employees leave
Keeping sensitive company data and information secure can be a major concern for businesses in a digital age. This is especially true when an employee leaves an organization, including termination. […]
5 Devices in your office that need protection
With cybercrime on the rise, even our office technology is at risk and can be targeted by a host of hackers, spyware, malware, viruses, and more. The following is a […]